The 2025 IC3 Report: The Staggering Data Behind Wire Fraud and BEC
In 2025, businesses lost billions to wire fraud and BEC - an epidemic the FBI says is hitting every industry.
The 2025 IC3 Report: The Staggering Data Behind Wire Fraud and BEC
The new 2025 IC3 Internet Crime Report makes one thing painfully clear: We are in an uphill battle; the frequency and severity of fraud is increasing.
What the 2025 IC3 report says:
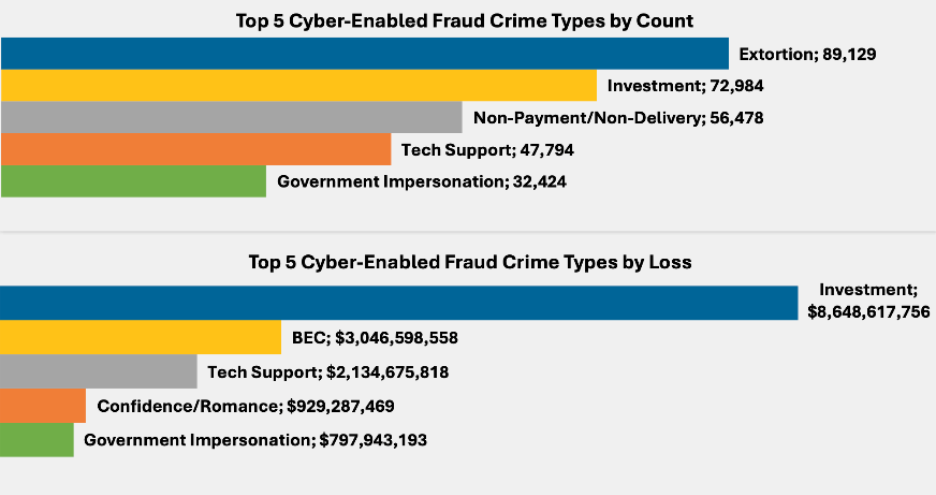
- IC3 logged more than 1 million complaints in 2025, with reported losses hitting a record $20+ billion
- Investment scams were the largest driver of reported loss at $8+ billion, followed by business email compromise at $3+ billion and tech/customer support scams at $2+ billion
- Cyber‑enabled fraud (the category where most wire fraud sits) accounted for just 45% of complaints but 85% of total losses - more than $17+ billion in 2025
From Conduit Security’s vantage point, that BEC number is the tip of the iceberg. On paper, BEC “peaks” at roughly $3 billion reported. In practice, the losses are much larger and often hiding in plain sight. The reported slice is small.
Of course, $3 billion is huge on its own, but it dramatically understates how much money is being lost to what we commonly refer to “wire fraud”. Various losses categorized in IC3 as “investment,” “real estate,” “romance,” “phishing/spoofing,” or “cryptocurrency” looks, in practice, like the same crime pattern Conduit Security is built to stop: a convincing message, a trusted relationship, and an irreversible transfer.
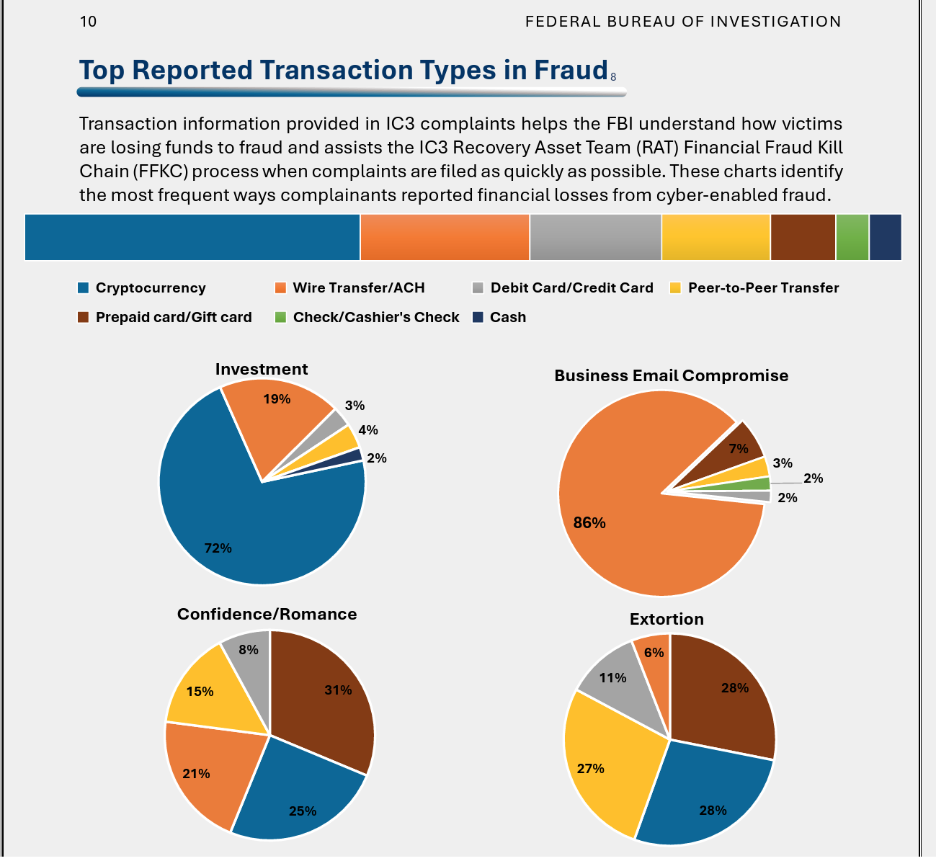
Another massive data point in the IC3 breakdown: about 86% of reported business email compromise losses travel over traditional wire and ACH rails, underscoring why securing high value payments is where the real risk and impact live.
Kill Chain as a hedge
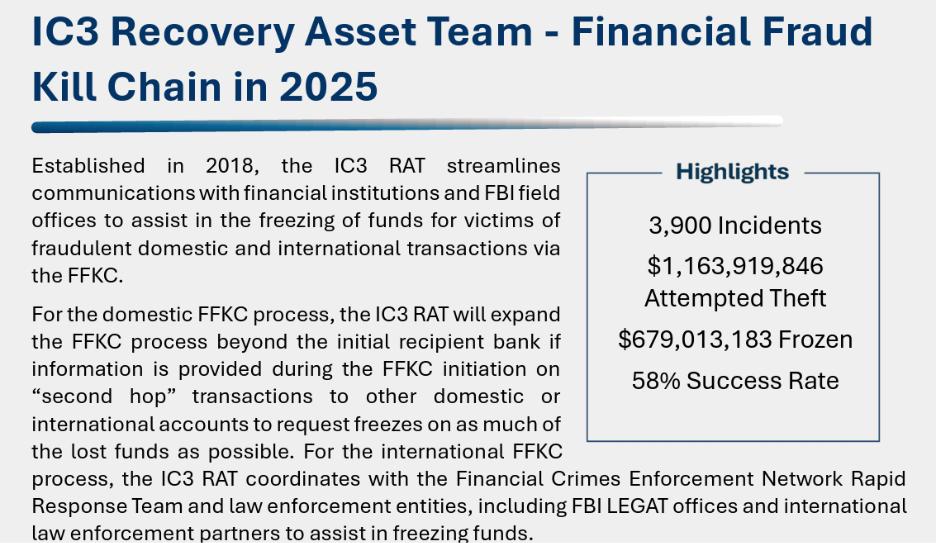
The IC3 Recovery Asset Team and Financial Fraud Kill Chain are a tremendous resource and continue to battle daily to help victims recover funds. Unfortunately, criminal behavior adapts and continues to make it harder to recover.
The reality:
- Time is everything. Once a wire lands, it doesn’t sit in an account waiting for someone to notice. Funds are broken up, bounced through additional banks or exchanges, or moved into crypto.
- Geography works against you. Many of these operations are run out of other countries, with layers of cutouts, shell companies, and low friction payment rails between you and the final destination.
- Process is slow by design. Law enforcement and bank partners must follow procedure with requests, verifications, coordination across time zones and legal systems. By the time the machine spins up, the much, it not all, of the money is often gone.
The Kill Chain is an important last‑resort response, not a control strategy. If your plan to manage wire fraud risk assumes you can lean on post‑transaction recovery, especially for cross‑border payments, you are betting against the clock and the organizational structure of these crews.
AI is now part of the attacker’s toolkit
One of the most notable shifts in this year’s report is how directly it calls out AI as an enabler of online crime. That shows up in two ways that are very relevant to BEC and wire fraud:
- Better emails, at scale.
Attackers no longer must be great writers or even fluent speakers of the target’s language to send clean, on‑brand, context‑aware messages. They can generate variants, A/B test subject lines, and tailor tone to “sound like” a CFO, a relationship manager, or a long‑time vendor.
- Deepfakes that validate the story.
When a wire is large enough, people look for extra assurance: a quick video call, a voice note, a short clip confirming that “yes, these new instructions are correct.” AI gives attackers the ability to fake all of that at a quality level that is good enough to get past a stressed, busy human trying to clear their queue.
The result is that all the old advice of looking for typos, weird grammar, or generic phrasing is rapidly losing value. Messages look right. Names, titles, and signatures are accurate. Audio and video can be manipulated. The only thing that really stands out anymore is that the payment request itself is unusual for the relationship.
What this means for teams moving real money
For companies and financial institutions that live in wires and high‑value transfers, the IC3 data reinforces a few uncomfortable but necessary truths:
- The biggest losses are concentrated in a cluster of fraud types that all share a BEC‑like pattern, whether or not they are labeled that way.
- The last mile controls around how payments are approved and released matter more than ever, because recovery remains uncertain, especially for overseas flows.
- AI is shrinking the gap between a sloppy scam and a professional‑looking request, which means content‑based detection and awareness training on “bad email tells” are losing their edge.
This is the problem Conduit Security is focused on: not blocking every bad email at the perimeter, but changing what happens at the decision point and when a real person is about to move real money.
If the IC3 report has a message for security, treasury, and operations leaders, it’s this: despite training, awareness, and well-defined processes, the effectiveness of this crime is increasing. Someone is trying to talk your people into sending money where it doesn’t belong. Your defenses need to include a technical control - a verification tool like Conduit is more necessary than ever.